Discover what strategic enterprises are doing to stay competitive using speech analytics.
Voice Analytics Blog
Featured Categories
PCI Compliance and Risk for Enterprise Telecommunications
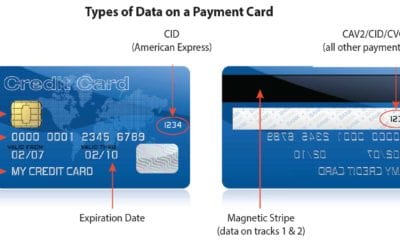
PCI - PII Redaction requirements Electronic data processing laws are constantly evolving and there are many standards and regulations that today’s businesses need to maintain. PCI - DSS, the International Payment Card Industry Data Security Standard, is a global...
PCI Overview
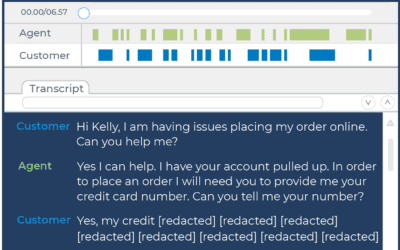
PCI Detection and Redaction for call center compliance
Call Center Data Security in the New World of WFH
The way call centers handle their data is crucial, and now that many around the globe will have to rapidly switch to a telecommuting model, they are faced with a whole new set of challenges.
How to Regulate Compliance with Speech Analytics
As access to sensitive consumer information proliferates, so does the number of attempts to compromise this data.
Compliance Monitoring: Harnessing the power of speech analytics
No matter your specific vertical, maintaining an intimate understanding of every voice interaction between customers and agents is integral for call centers to maximize revenue, retention rates, and customer security.
Why PCI Redaction Matters: Creating a Queryable Database of Customer Insight
It doesn’t matter if you’re running a multibillion dollar giant like Equifax or a small mom-and-pop shop—data security breaches can happen to anyone. If you are accepting credit cards as a form of payment or collecting any other type of personal information, you have taken on the burden of protecting that information for your customer.
5 Benefits of Being PCI Compliant
WHY IS IT IMPORTANT TO BE PCI COMPLIANT?
The Payment Card Industry Data Security Standard (PCI DSS) is a set of rules and regulations around credit cards, sensitive payment data, and other identifiers. Merchants are subject to $25+ fines per card leaked, suspension of merchant privileges, and mitigation costs that could skyrocket into millions of dollars for even a small data breach.
Why PCI Compliance Matters
Businesses are no longer just physical places, but virtual ones that can be accessed, and breached, anywhere at any time from multiple devices.